Scalable, Flexible, and Reliable Security
The virtual universe is expanding into a dense web of interdependence—increasing the environment’s complexity and making it challenging to manage security effectively. Fortunately, there are many prospects out there that have helped us unravel the problem. Cybersecurity mesh, one of the year’s most buzzed-about concepts among industry watchers, is a defense strategy that involves giving every piece of hardware and every key access point their protective barrier.
The Cybersecurity Mesh is considered one of Gartner’s “Top security and risk management trends for 2022“. The report claims that the upsurge of remote work amid the pandemic has created new attack vectors. As digital transformation continues, it will become increasingly important to implement security measures that can be easily scaled to accommodate distributed workforces, edge computing devices, virtual networks, and IoT technologies. The conclusion was that a comprehensive, interconnected, and robotic cybersecurity mesh architecture is the solution to this issue.
Cybersecurity Mesh
Cybersecurity mesh-defined as a distributed architectural strategy for achieving scalability, flexibility, and dependability in cyber control. By shifting attention away from securing a centralized IT perimeter, the mesh allows for a more decentralized cyber security policy orchestration and enforcement system. By this, the network administrators can provide varying degrees of access to different constituents and assets while also making it more difficult for cybercriminals and hackers to exploit the entire network by constructing smaller, individual perimeters that protect distributed access points.
The Cybersecurity Mesh Architecture
A cybersecurity mesh architecture (CSMA) aims to create a more unified security policy by encouraging communication and cooperation among various security measures—improving overall security by focusing on protecting individual endpoints rather than trying to secure an entire organization’s assets with a single technology. As its name suggests, CSMA is meant to facilitate the transition from disparate, outdated systems to a more unified whole.
The question is how we can make progress toward this objective.
- Network security could be more adaptable with CSMA’s facilitation of communication and integration among disparate security services.
- A more adaptable security posture can be achieved through CSMA implementation in your business. CSMA solutions provide a more versatile and scalable countermeasure against the growing threat of digitalization.
- With CSMA, cybersecurity tools can be easily deployed and maintained promptly. It helps you save money, time, and effort by reducing the need to purchase and implement security measures for which there is only a short-term requirement.
- You can strengthen your defenses with the help of CSMA because it promotes communication between your various analytical and integrated security tools. Because of this, you’ll be better able to deal with intrusions and attacks.
Do you know
By 2024, Gartner predicts that businesses using CSMA will reduce the average financial impact of a cyber incident by 90%.
Thus, integrating it into your system is a must for any business. Here is why.
Cybersecurity Mesh for Today’s Businesses
Fortune Business Insights predicts the global cybersecurity market will reach $375 billion by 2029. Enterprise resources are increasingly located outside an organization’s localized security perimeter, and growth trends indicate that businesses of all sizes must be agile enough to expand rapidly without compromising network security. As companies extend beyond a single location, every computer connected to the network becomes a potential weak spot. Cybercriminals are increasingly utilizing these weak points to launch ransomware and other forms of malware.
Do you know
Estimated annual losses caused by cyberattacks are close to $6 trillion. A value of that magnitude is genuinely shocking.
When dealing with these threats at the enterprise level, the most effective and versatile strategy is to implement a cybersecurity mesh. By incorporating it into your overall design, you can protect every part of your infrastructure from every angle. In addition, a cybersecurity mesh can adapt to new threats over time because the most up-to-date threat intelligence fuels it.
Importance of Cybersecurity Mesh
1. Zero Trust Access
The cybersecurity mesh is an essential part of the zero-trust network philosophy, in which no endpoint is automatically trusted when attempting to connect to a local area network. When it comes to protecting a network, focusing solely on its perimeter is often ineffective, as studies have shown that as much as 34% of data leaks and breaches start within the network itself. For real-time threat detection and protection of valuable data and devices, a distributed cybersecurity mesh that employs zero trust is preferable to a traditional VPN(virtual private network) login. This offers ease in adapting to new threats and changing access requirements also. The mesh guarantees the same high level of protection for all data, systems, and equipment, regardless of their physical location within the network or beyond. Until the security protocol verifies it, any connection to access data is assumed to be “unreliable.”
2. Development of IT
Traditionally, cybersecurity meant constructing a password-protected perimeter so only authorized devices could connect to a network and handling security permissions. The advent of the cybersecurity mesh approach demands a fundamental reorganization of IT infrastructure, incorporating several different safeguards at the outset of network design. Security will be shifted “to the left,” or to the development team, to allow for more agile deployment in the long run. IT security is built into the plan from the start of the process when the network’s infrastructure is conceived.
3. Defending Software and Networks
Businesses are using microservices more and more. Microservices are an architectural style that builds apps as a group of loosely connected, independently delivered services instead of as one big service. Incorporating a zero-trust strategy into the mix and protecting these applications in a cybersecurity mesh improves efficiency and visibility. The idea of a service mesh is also gaining traction when deploying large-scale applications in an enterprise setting.
For instance, the following are all attacks that can be defended against:
- Service impersonation – when a hacker gains access to a private application network and poses as a legitimate service to request sensitive information.
- Unauthorized access – when a service request, though legitimate, attempts to access private information without proper authorization.
- During packet sniffing – when an attacker impersonates a legitimate user to gain access to their data.
- Data exfiltration – when sensitive information is intentionally leaked outside a safe system.

Use Cases for Cybersecurity Mesh
Now that the concept of it is understood, let’s look into how can it be applied. Cybersecurity mesh can be used in many different contexts, improving an organization’s security by making it more versatile and adaptable. For instance, this method in IT development helps a company streamline its approach to managing security policies. This could be achieved by developing a system that can be applied independently to different architectural styles, facilitating adaptability and growth.
CSMA also allows you to upgrade your security setup by incorporating it into your network by using tools for all incoming and outgoing traffic making your network safer by design. This enhances to,
1. Future-proof yourself: Selecting cybersecurity technologies that allow for integration will put your company in a superior position to deal with potential future security threats. Extensible analytics, for instance, can be modified and expanded through plug-in application programming interfaces (APIs).
2. Eliminate the voids: Security holes caused by insufficiencies or flaws in various solutions can be patched by adopting modern and future-state security practices.
3. Utilize CSMA-based layering: Security analytics, an identity fabric, policy management, and consolidated dashboards are just a few of the CSMA’s enabling technologies that should be exploited. The sum of these parts can be an all-encompassing security system if they are integrated into a whole.
Financial services, healthcare, and the government all have a pressing need for cyber security measures. Recently, healthcare sectors are adopting cybersecurity mesh for the reasons here.
Cybersecurity Mesh for Healthcare
Many hospitals face a significant challenge when consolidating data due to the complex nature of their infrastructure, which consists of many separate systems and teams. The Internet of Things (IoT) and new technologies make it easier to attack, and the use of distributed administrative and IT teams makes the situation even more complicated. Even in the first half of 2022, the number of ransomware attacks on the healthcare industry increased by a shocking 328%. In light of these cyber threats and the ever-increasing number of analyst-proposed methods and acronyms offered to boost security, developing the most effective cyber strategy for an entire health system can be daunting.
Organizations must “never trust, always verify” user authentication at every entry point in this situation. Zero Trust Access (ZTA) recommends a unified structure for deploying security measures like identity verification and multifactor authentication (MFA) to stop lateral network movement. If implemented carefully, ZTA can boost efficiency and security. Some healthcare delivery organizations use a patchwork of solutions to reach ZTA, but this isn’t the most streamlined or long-term-friendly process. A system that serves CISOs and ends users needs robust technology integrations.
Lucky for us, there’s a new analyst term that expands on ZTA to advocate for this: cybersecurity mesh architecture (CSMA).
Thus healthcare organizations who want to strengthen their digital identity and access point defenses beyond what zero trust can provide, are looking into implementing a cybersecurity mesh.
Do you know
Due to the increased adoption of IoT devices and financial investments, it is predicted that North America will dominate the revenue share over the other regional markets in the cybersecurity mesh industry.
CSMA guidelines for CISOs and CIOs
If your company is considering adopting this architecture to improve its shields, here are a few points.
1. Start With a Zero-Trust
A CSMA is one of the fundamental components of a zero-trust setting. This method ensures that all data, systems, and equipment can be accessed securely, no matter where they are. It also helps threats to be found in real-time and dealt with quickly. Therefore, adopting a zero-trust mentality at the outset is crucial for a smooth rollout.
2. Adopt Microservices
Microservices can help prevent hackers from taking advantage of a network’s vulnerability in a single node by enforcing individual security policies on each node. Engineering teams can use microservices to implement the mesh early in the planning process, taking the necessary precautions against potential and actual threats.
3. Permit a Complete Reset of Cybersecurity
One of the best ways to guarantee the success of your CSMA is to allow for a complete reorganization of cybersecurity. Such a reorganization can let you integrate security early on—rather than as an afterthought—without resorting to password-protected perimeters to let devices connect to a network. Security can be deployed more flexibly and effectively across a distributed workforce if it is shifted further to the left.
4. Get ready for a possible migration
The rapid adoption of cloud computing has been driven by the need to serve customers better and end users. But it can also lead to security holes. The cybersecurity mesh allows for the transition because it offers cloud computing environments protection that can be acclimated to fit their needs.
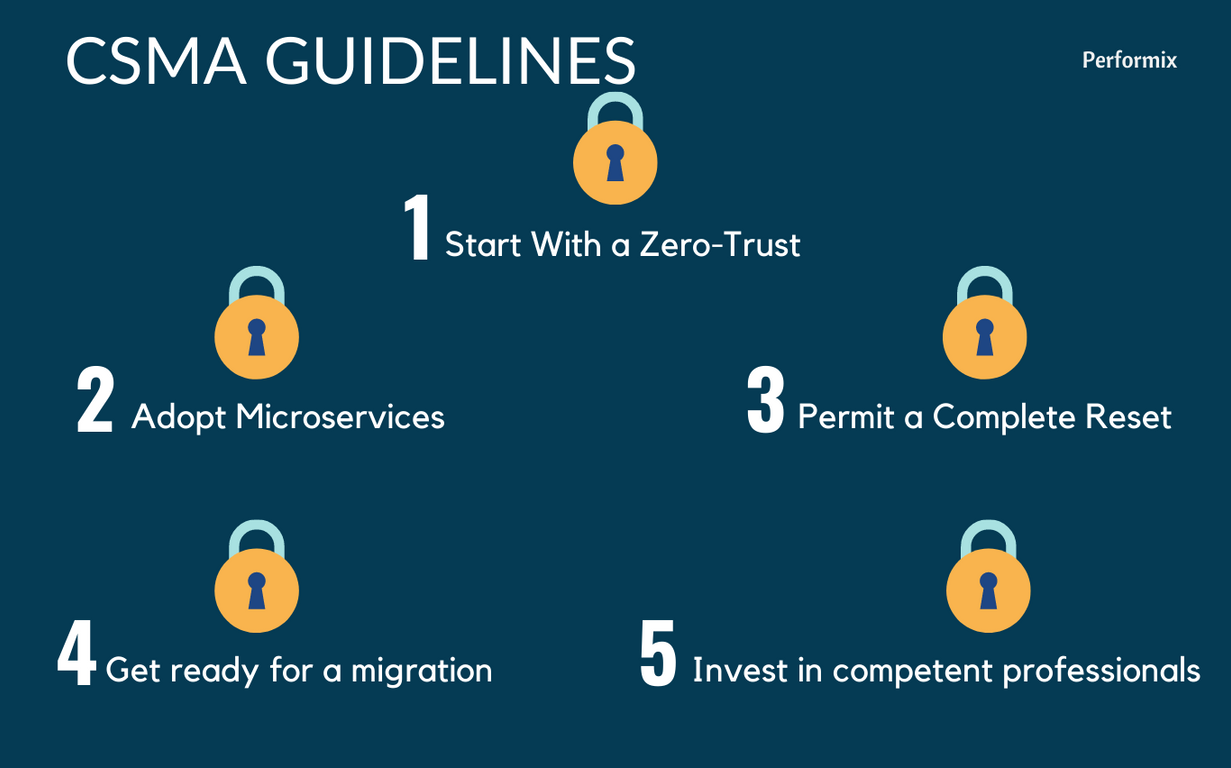
5. Invest in competent professionals
Investing in highly skilled security professionals is a good idea if you want to see quick results from your cybersecurity mesh architecture. Experts in this field can implement a mesh architecture tailored to your company’s needs and objectives, freeing you to concentrate on business expansion rather than the security and privacy concerns associated with your remote workforce.
Secure your company’s data
The risks posed by cyberattacks have increased due to the opportunities presented by the COVID-19 pandemic. Further, the quickening pace of digital innovation and transformation has led to a whirlwind of change in the information technology requirements of businesses and organizations of varying sizes. It has become significantly more difficult and complex to keep up with existing threats while adequately preparing for zero-day threats. Using a modular security approach, centralizing policy orchestration, and distributing policy enforcement, a cybersecurity mesh architecture can ensure that enterprise data is safe and secure. This is particularly important in today’s age of hybrid work when it is more important than ever to protect enterprise data.
To help your business scale effectively in an ever-evolving digital environment, we provide security-driven networking, zero-trust access, and adaptive cloud security. As a result, the mesh is greatly simplified through automation, and speed and efficiency are greatly improved. When it comes to managing the entirety of the digital attack surface, Performix is up to the task, able to close any security loopholes and reduce the likelihood of a breach.